Tips on how to identify a fraudulent transaction
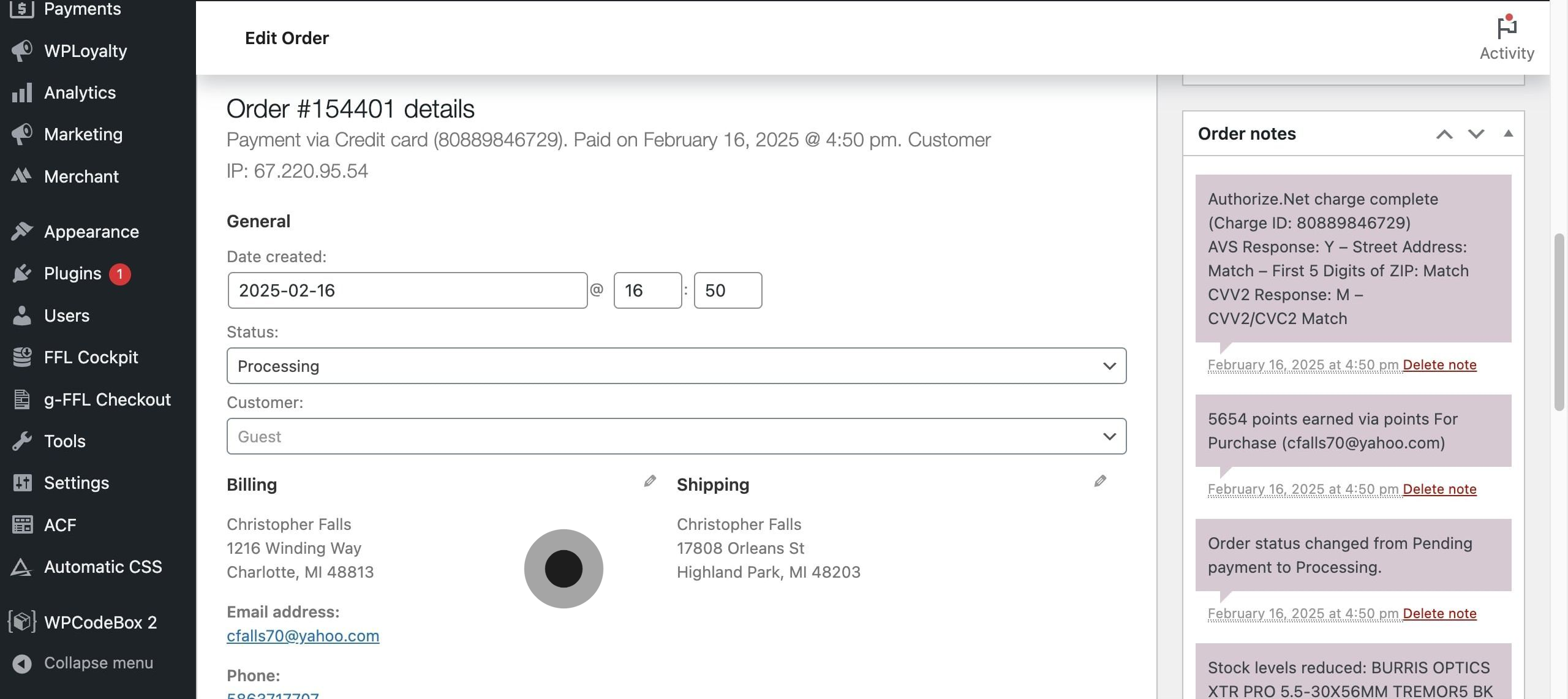
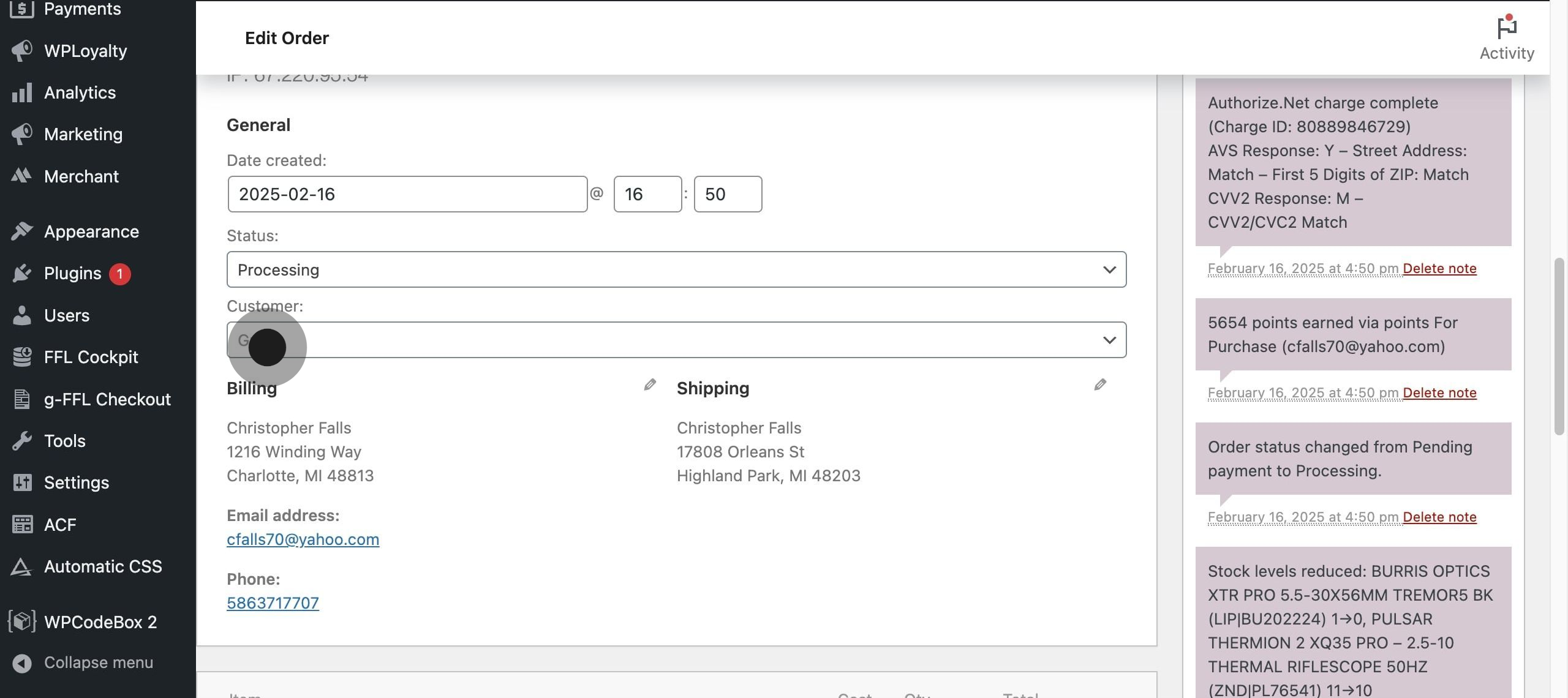
1. **First, verify the customer's identity by cross-referencing their provided information. Pay special attention to the email address - legitimate customers typically use personal or business email addresses rather than temporary or free email services.**
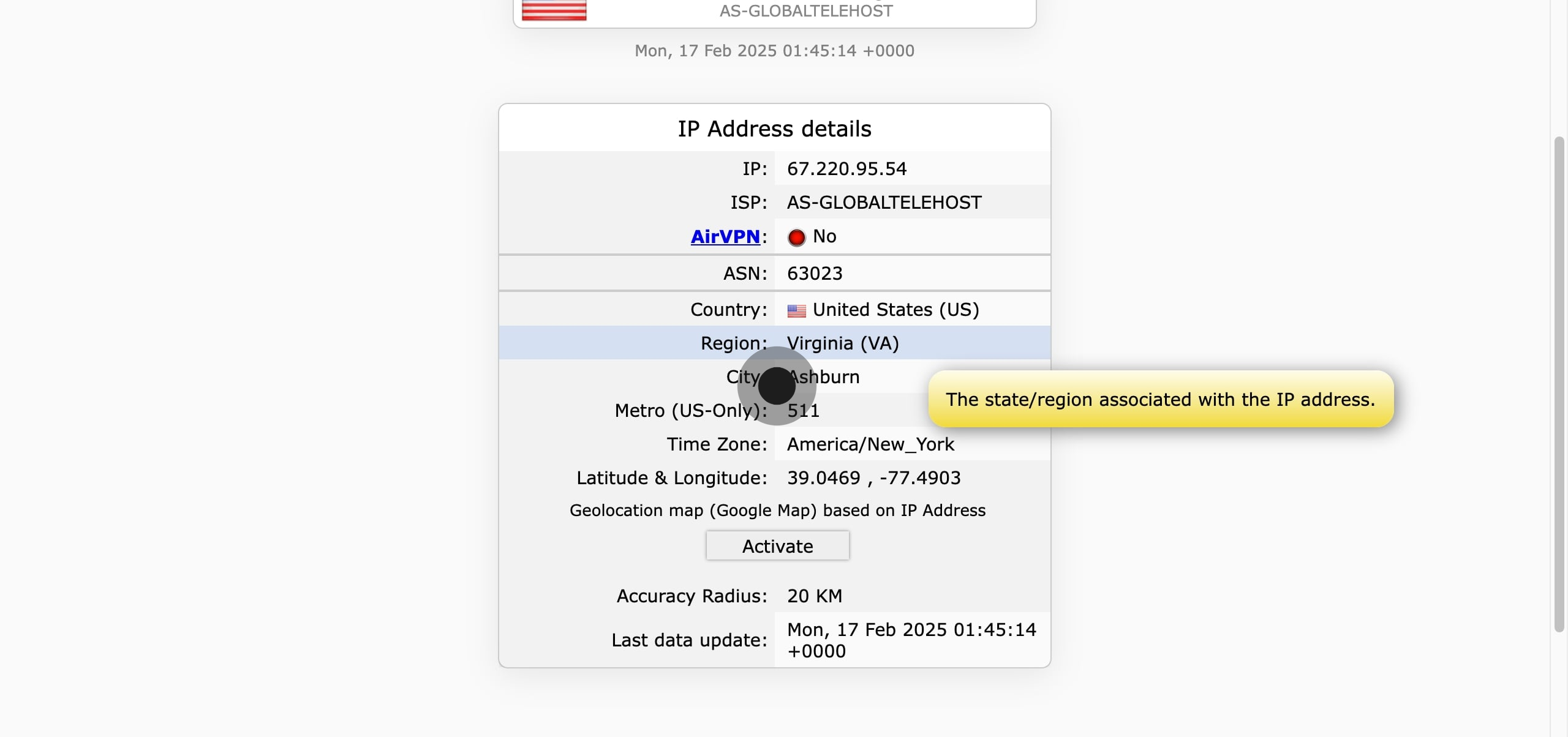
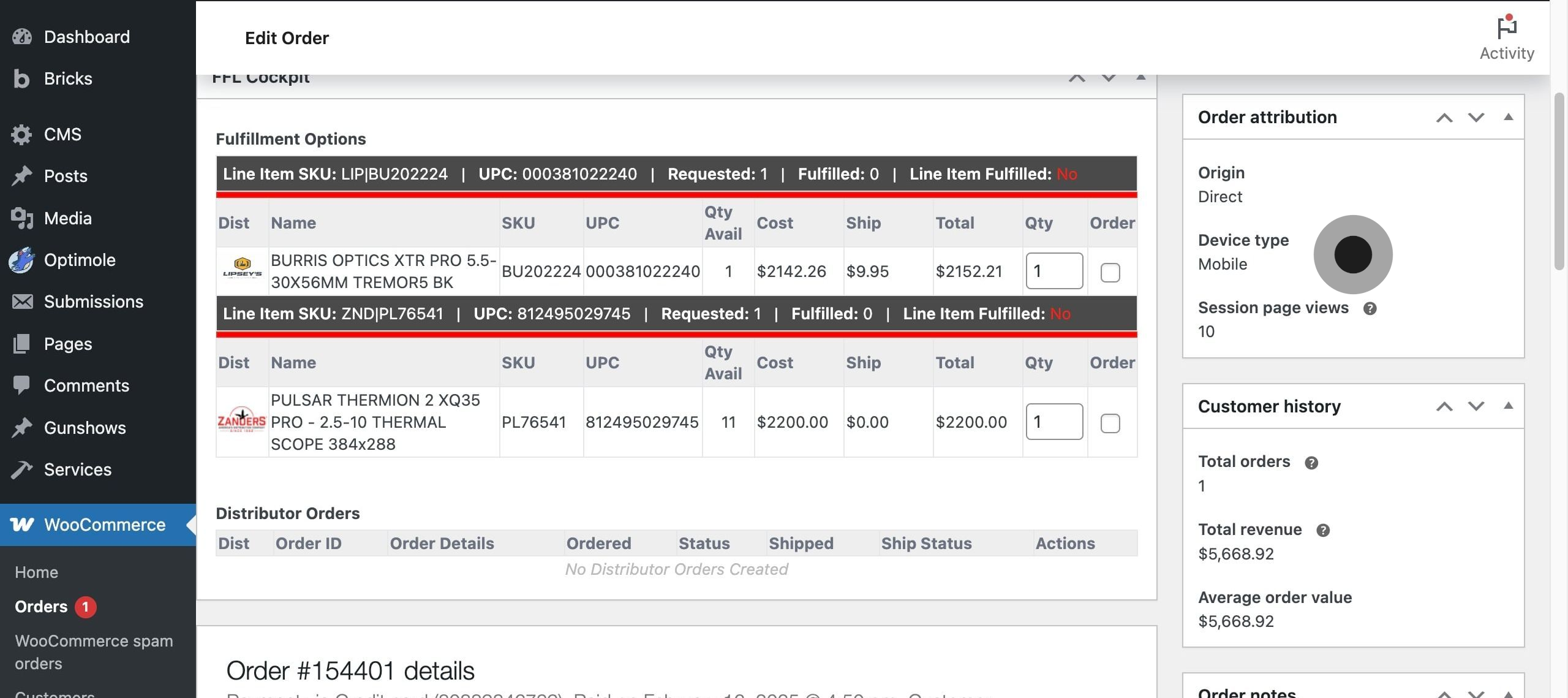
2. **Another effective verification method is examining the IP address associated with the order.**
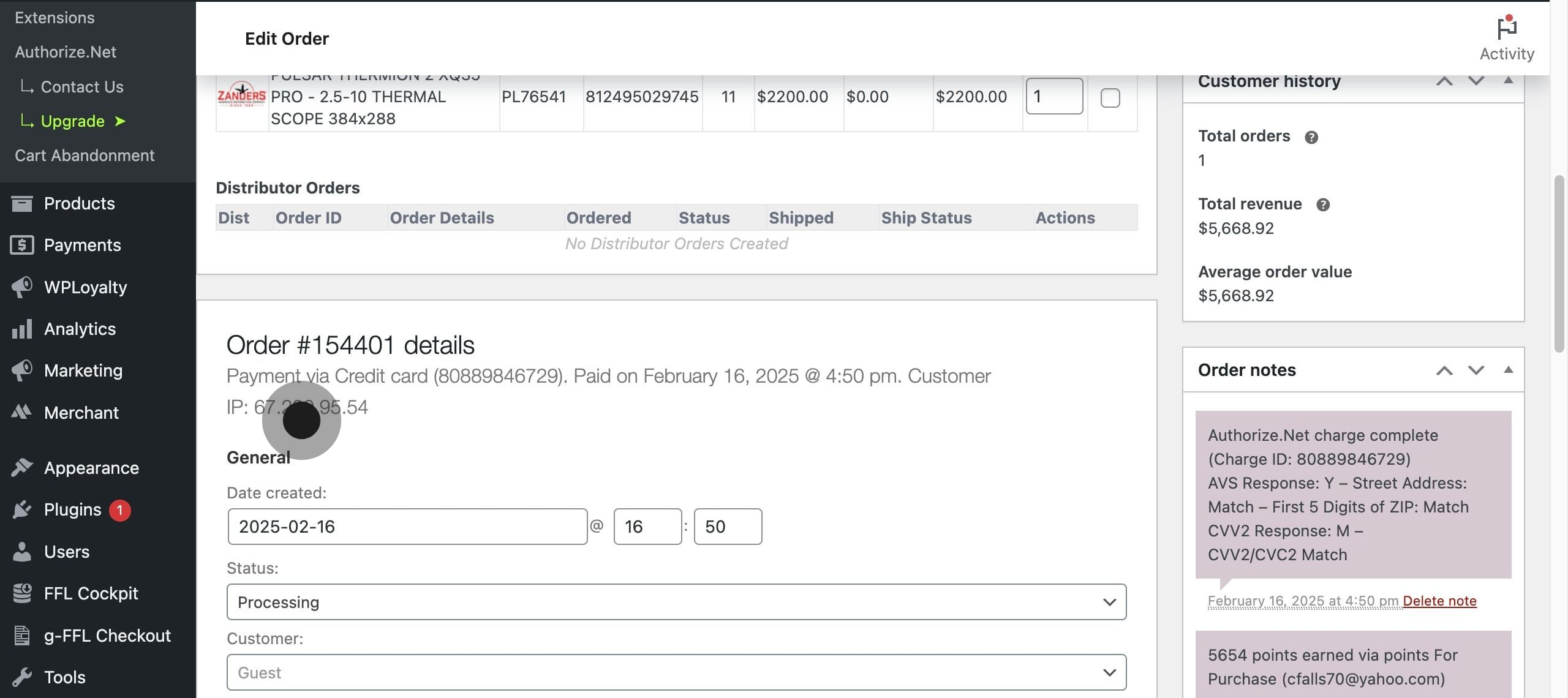
3. Click on the element.
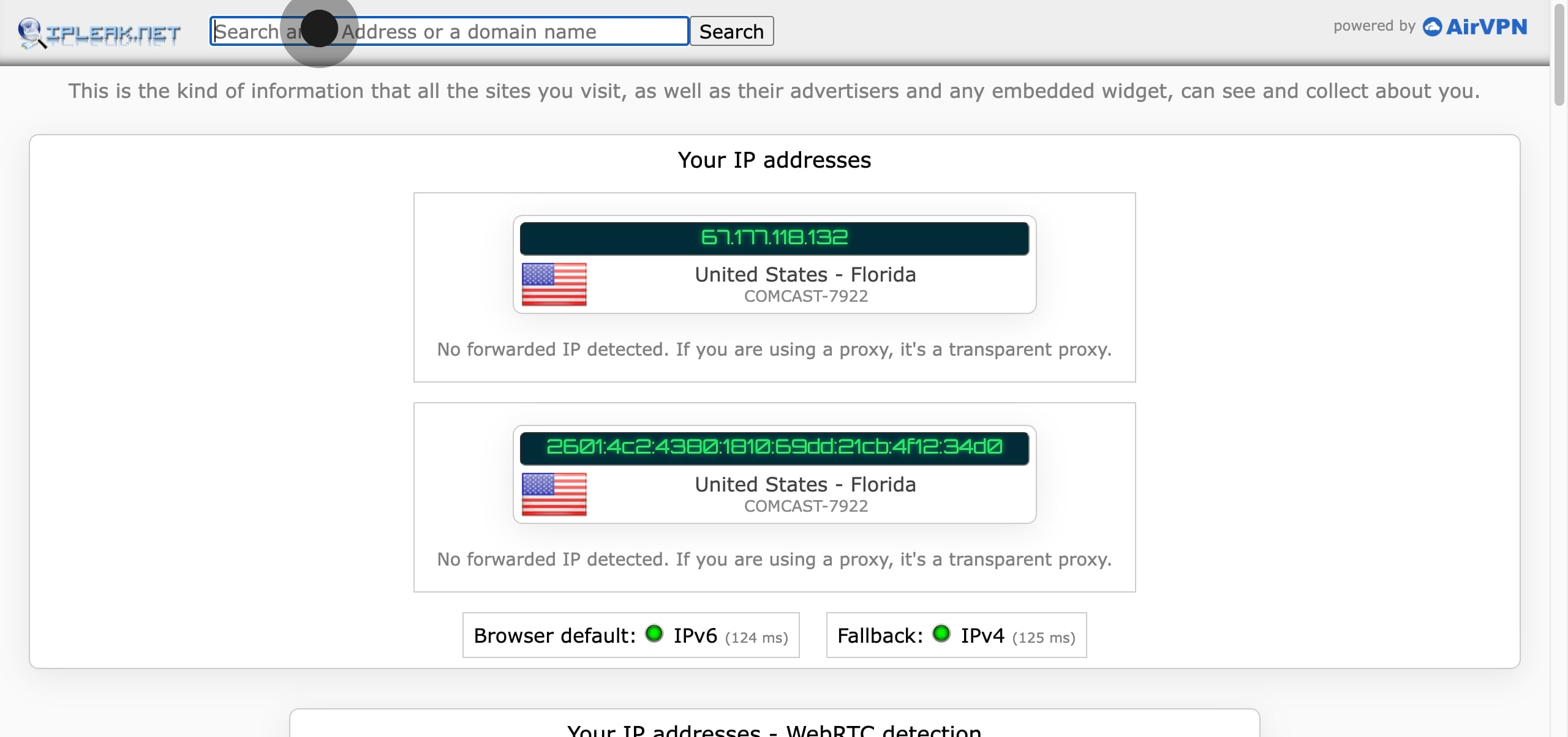
4. Search for the customer IP
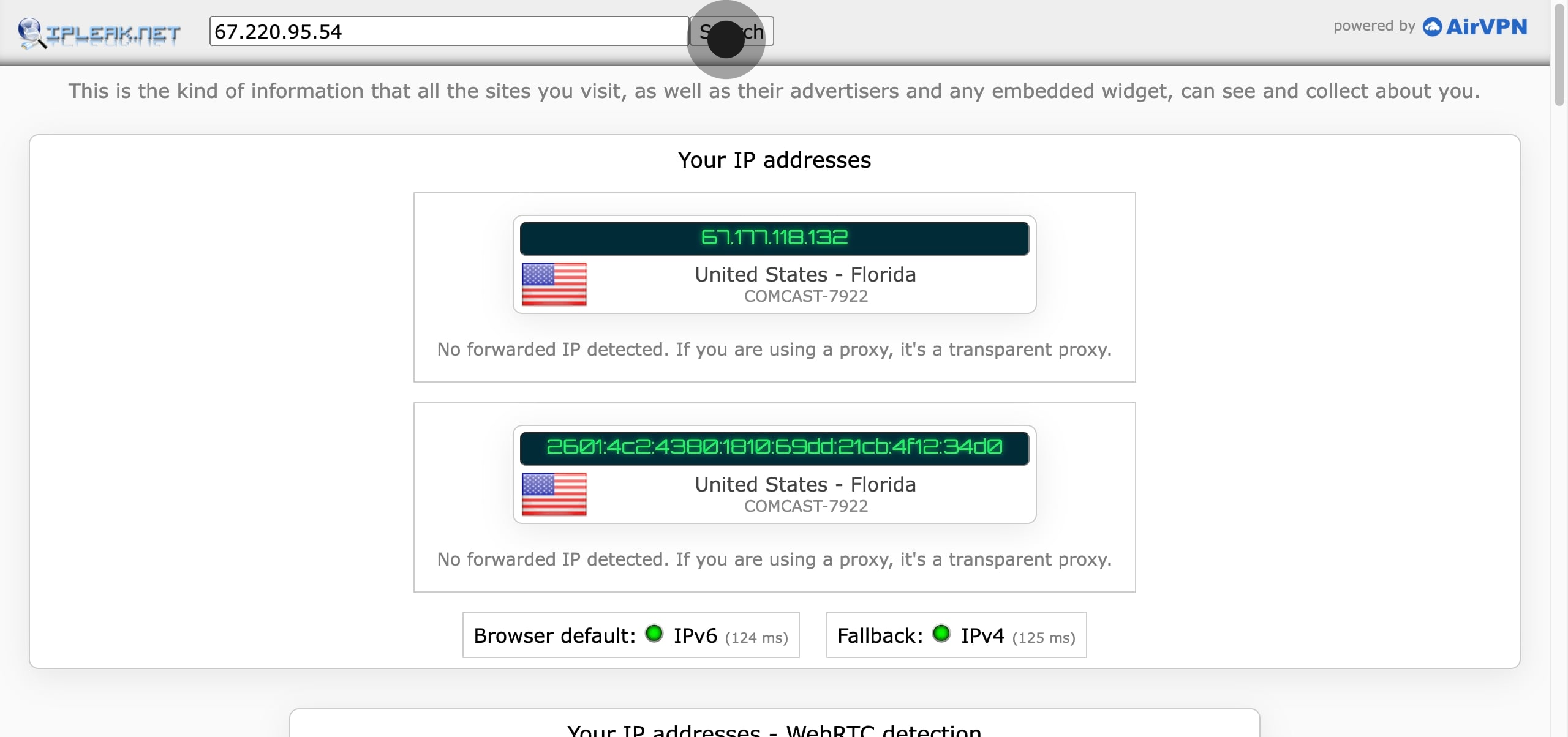
5. **If the IP location differs significantly from the billing or shipping address without a reasonable explanation, this could indicate potential fraud. Remember that some legitimate customers may use VPNs or place orders while traveling.**
6. Guest checkout orders require extra scrutiny since they lack the transaction history and security measures of registered accounts.
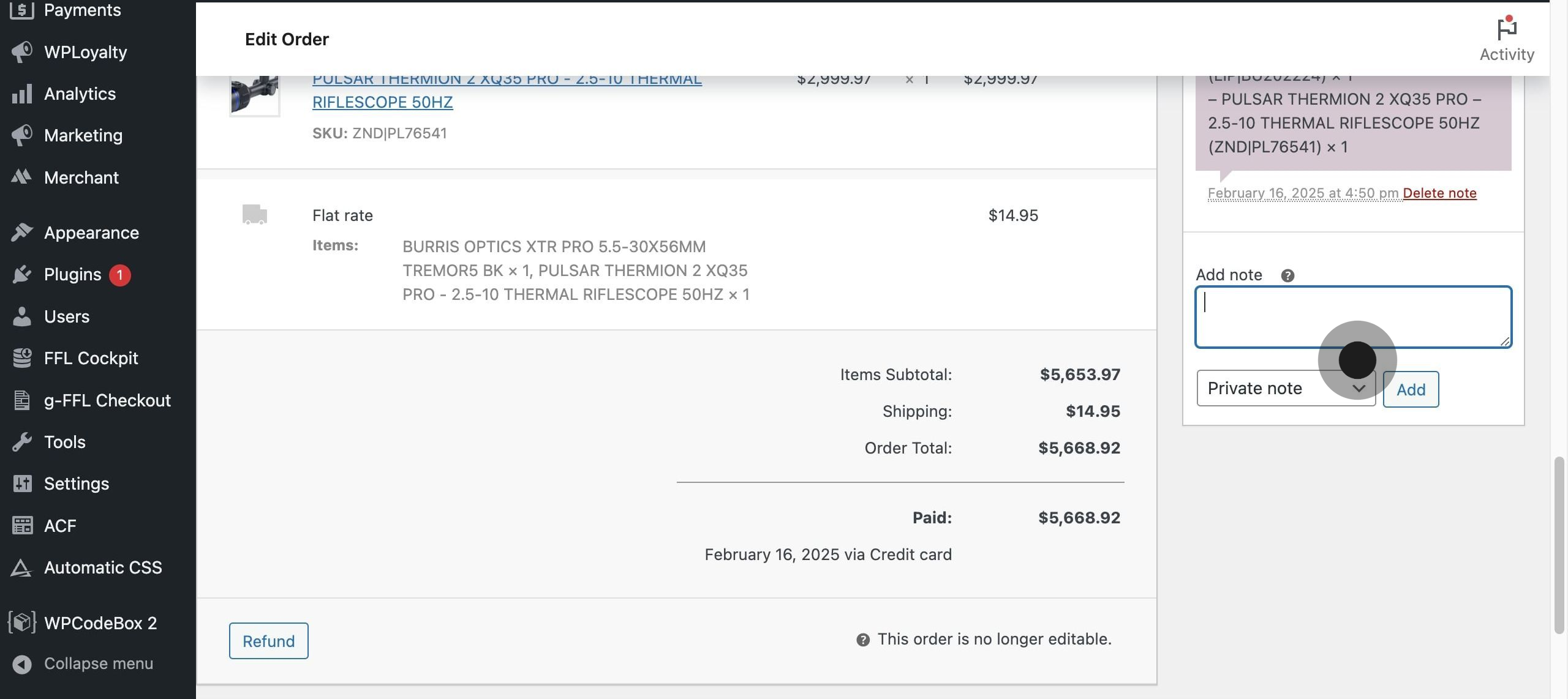
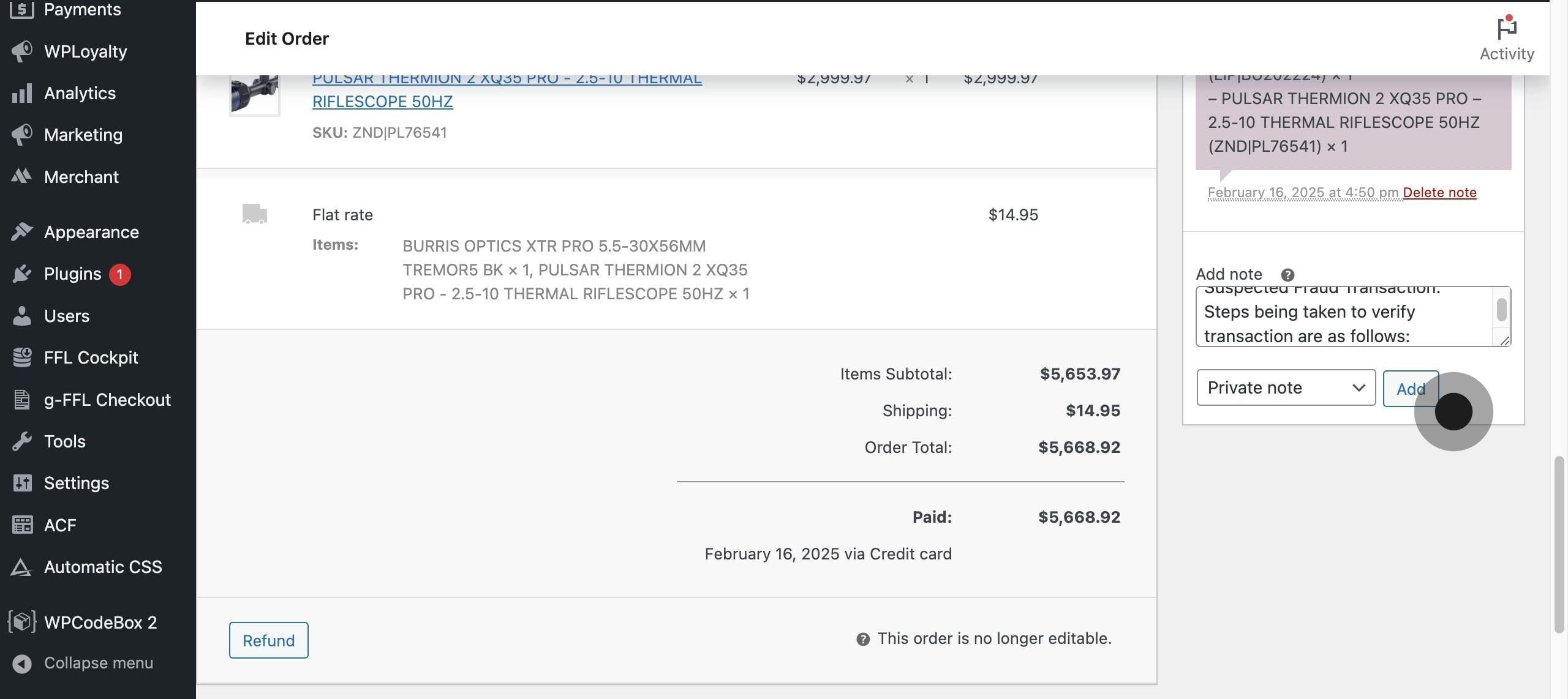
7. Keep detailed records of any suspicious patterns or confirmed fraudulent orders to help identify similar attempts in the future. This documentation can help you refine your fraud detection process and may be valuable if you need to dispute chargebacks or file reports with law enforcement.
8. Then, click on "Note type".
9. Click on "Origin".
Tips on identifying fraudulent accounts:
When processing orders through your e-commerce website, you may occasionally encounter transactions that raise suspicion of fraud. Fraudulent orders can result in significant financial losses, chargebacks, and damage to your business reputation. To protect your business and legitimate customers, it's crucial to have a systematic approach for verifying suspicious transactions.
Key warning signs that may indicate potential fraud include mismatched shipping and billing addresses, unusually large orders, multiple failed payment attempts, or orders using high-risk shipping methods. Understanding these red flags enables you to implement effective verification procedures. Let's examine several proven methods to help determine whether an order is legitimate:
First, verify the customer's identity by cross-referencing their provided information. Check if the billing address matches what's on file with the credit card company. Pay special attention to the email address - legitimate customers typically use personal or business email addresses rather than temporary or free email services. Contact information should be consistent across all order details.
For orders that raise multiple red flags, consider implementing additional verification steps such as calling the customer directly using the phone number provided with the order. A legitimate customer will generally be happy to verify their purchase, while fraudsters often provide false or disconnected numbers. You can also send a confirmation email requiring a response before processing the order.
Another effective verification method is examining the IP address associated with the order. If the IP location differs significantly from the billing or shipping address without a reasonable explanation, this could indicate potential fraud. However, remember that some legitimate customers may use VPNs or place orders while traveling.
Keep detailed records of any suspicious patterns or confirmed fraudulent orders to help identify similar attempts in the future. This documentation can help you refine your fraud detection process and may be valuable if you need to dispute chargebacks or file reports with law enforcement.
Guest Accounts:
Guest account orders warrant extra scrutiny because fraudsters often prefer them to avoid creating trackable user profiles. Let me explain why guest checkouts can be riskier and how to properly evaluate them.
When customers create dedicated accounts on your e-commerce platform, they establish a transaction history and provide verified contact details that become part of their digital footprint. This history helps build trust and makes it easier to spot unusual behavior. For example, if a customer with a regular account suddenly places an order that deviates significantly from their typical purchasing pattern, it raises an immediate red flag.
In contrast, guest checkouts provide minimal historical context for verification. Fraudsters exploit this limitation by using guest accounts to make one-time purchases, knowing they won't leave behind a traceable pattern of behavior. They can freely enter different names, addresses, and payment information for each transaction without raising the automatic flags that would trigger in a registered account showing sudden changes.
Consider this scenario: A fraudster obtains stolen credit card information and wants to make unauthorized purchases. By using guest checkout, they can:
1. Avoid the email verification typically required for account creation
2. Bypass any account security measures like two-factor authentication
3. Prevent the legitimate cardholder from discovering the unauthorized charge through account notifications
4. Make multiple fraudulent purchases across different websites without establishing patterns
To properly evaluate guest checkout orders, implement these verification steps:
Compare the IP address location with the shipping and billing addresses. While legitimate customers occasionally place orders while traveling or using VPNs, significant geographical discrepancies in guest checkouts deserve closer examination. For instance, if an order ships to New York but comes from an IP address in a high-risk country known for fraud, that's cause for concern.
Examine the email address provided during guest checkout. Legitimate customers typically use established email addresses, while fraudsters often create temporary or disposable email addresses. An email address that appears randomly generated (like "jk4hr8x@tempmail.com") should raise suspicion, especially in combination with a guest checkout.
Look for multiple guest orders using the same payment method but different shipping addresses, or vice versa. This pattern often indicates a fraudster testing stolen card information or attempting to distribute fraudulent purchases across multiple locations to avoid detection.
Consider implementing additional verification steps specifically for guest checkouts, such as:
- Requiring CVV verification for all guest transactions
- Setting lower transaction limits for guest orders
- Implementing more stringent address verification services (AVS) checks
- Sending order confirmation emails that require a response before processing
- Adding CAPTCHA or similar human verification steps to the guest checkout process
Remember that while guest checkouts can indicate higher fraud risk, many legitimate customers prefer guest checkout for valid reasons, such as convenience for one-time purchases or privacy concerns. The key is to balance fraud prevention with customer experience by applying these verification methods systematically rather than treating all guest checkouts as suspicious.
Keep Detailed Records:
Keep detailed records of any suspicious patterns or confirmed fraudulent orders to help identify similar attempts in the future. This documentation can help you refine your fraud detection process and may be valuable if you need to dispute chargebacks or file reports with law enforcement.
Was this article helpful?
That’s Great!
Thank you for your feedback
Sorry! We couldn't be helpful
Thank you for your feedback
Feedback sent
We appreciate your effort and will try to fix the article